Researcher Exposes Rootkit-Level Threats in Windows Path Conversion Flaws at Black Hat Asia
April 23, 2024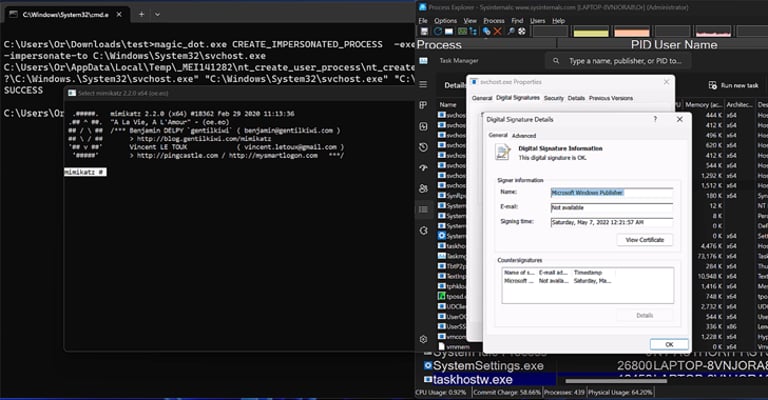
At the Black Hat Asia conference, SafeBreach researcher Or Yair revealed vulnerabilities in Windows path conversion could lead to rootkit-like control.
Yair's research exposed multiple vulnerabilities, such as remote code execution and elevation of privilege, by exploiting flaws in DOS-to-NT path conversion.
The security gaps enabled Yair to conceal files and processes and interfere with system tools like Task Manager and Process Explorer.
Microsoft has addressed some of the vulnerabilities reported by Yair and acknowledged the existence of others.
This research underscores the critical need for addressing known issues that might be exploited for significant security breaches.
Summary based on 2 sources
Get a daily email with more Tech stories
Sources

The Hacker News • Apr 22, 2024
Researchers Uncover Windows Flaws Granting Hackers Rootkit-Like Powers
Security Affairs • Apr 22, 2024
Windows DOS-to-NT flaws exploited to achieve unprivileged rootkit-like capabilities